By Appointment Only
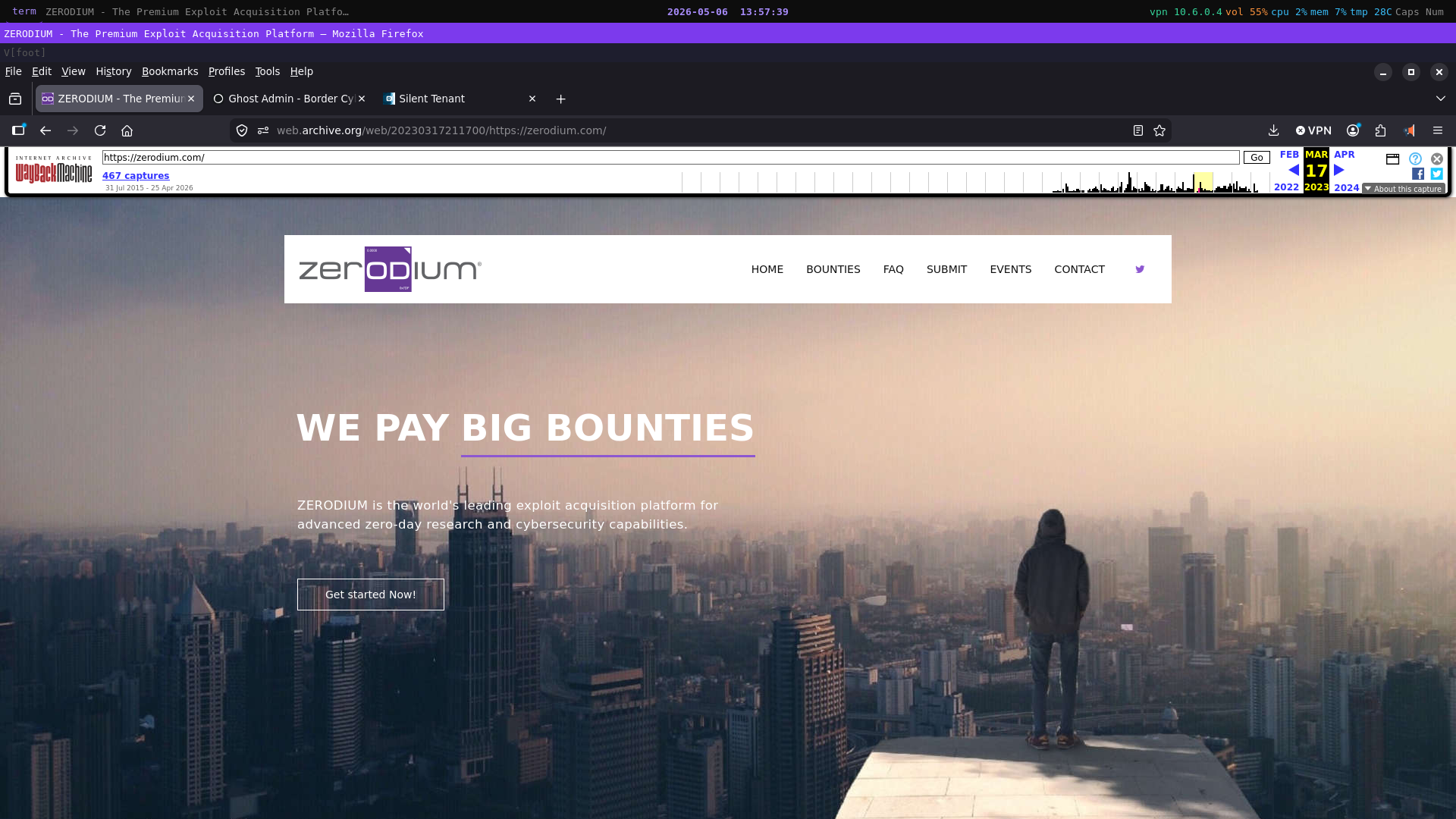
There once was a website. It had clean typography, a professional layout, and a price list. The price list told you that a zero-click exploit chain for Android would cost you two and a half million dollars. iOS, two million. Windows, WhatsApp, Tor — the menu had you covered. Everything tastefully formatted. No fine print about intended use. No disclaimer about end-users.
The company was called Zerodium. It was incorporated in Delaware. It had a LinkedIn page.
But here is what the website was not: an invitation to browse. Chaouki Bekrar, Zerodium's founder, said it himself when he published that price list in 2015 — "The first rule of the 0days biz is to never discuss prices publicly. So guess what: We're going to publish our acquisition price list." That sentence rewards close reading. It is not the language of a man opening a shop. It is the language of a man throwing a gauntlet. The publication of prices in a market that runs entirely on secrecy and personal relationship was itself the communication — a signal fired simultaneously at two audiences who would never meet each other.
To the researchers: we are capitalised, we are serious, and we will pay you more than anyone else on earth.
To the government clients: the inventory is real, the operation is disciplined, and we are not afraid of you.
Everyone else — journalists, regulators, civilians who stumbled across the URL — was not the audience. They were the backdrop. The price list that looked like transparency was functioning as credential. Proof of institutional seriousness, dressed in the clothes of openness, readable only by the people with sufficient context to understand what they were actually looking at.
The price list was the acquisition side — what Zerodium paid researchers for working, weaponisable zero-day exploits. What it did not publish, and what the public record has never fully resolved, was the precise structure of the client-side arrangement. What we know is this: government clients subscribed, at a minimum of half a million dollars annually, to something Zerodium called the Zero-Day Research Feed. What that subscription purchased was not, in all likelihood, the weapons themselves. It purchased a seat at the table where the weapons were described — access to the catalogue, knowledge of the inventory, intelligence about what offensive capabilities existed and against which platforms. The weapons themselves, the deployable exploits, were almost certainly a second transaction: exclusive acquisitions, priced separately, with exclusivity not as a premium feature but as the technical precondition of the weapon's value. A zero-day distributed to multiple clients ceases to be a zero-day. It becomes a liability. The mechanics of this architecture — and what they reveal about who the clients actually were and why — are worth examining with some care.
This is the phase that the Wayback Machine preserves: the years of the public price list, the LinkedIn page, the professional typography. The years during which Zerodium conducted what was, in any honest accounting, an international weapons market — in full view, without regulatory interference, without serious legal exposure in any jurisdiction — because the entities with the power to close it were also the entities writing the subscription checks.
Then, in late 2024, the website went quiet. No updates. No pricing revisions. No confirmation of active acquisitions. The operation that had spent nearly a decade being conspicuously, almost aggressively visible simply — stopped updating its window display.
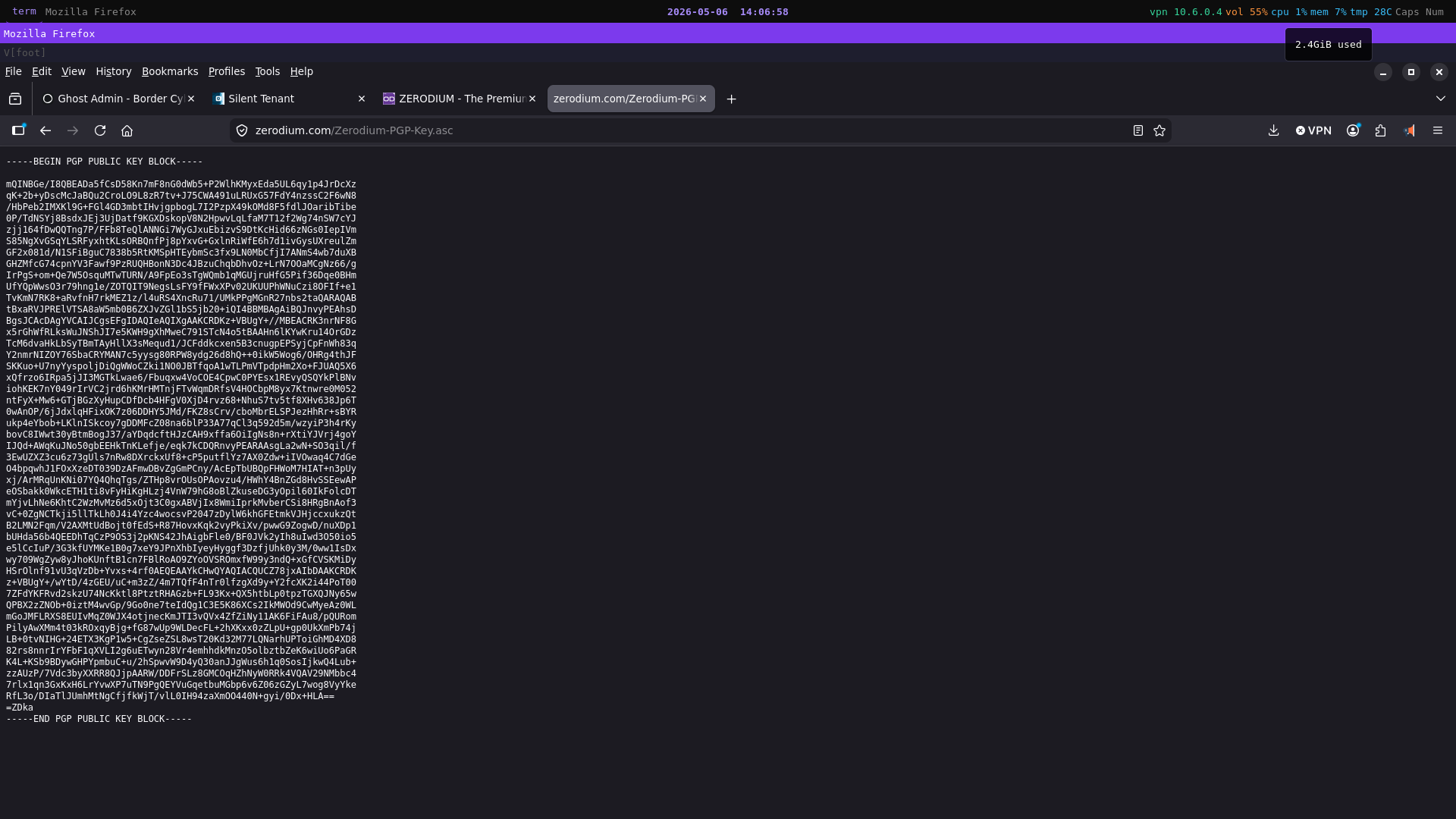
In January 2025 the window came down entirely. What replaced it was a single page: an email address, and a PGP public key.
This is the detail that the trade press noted with puzzlement and then moved on from. It should not be moved on from. A PGP key is not a door. It does not lock anyone out in any conventional sense. What it does is filter — instantly, completely, and without explanation — everyone who lacks the technical literacy to know what a PGP key is and how to use one. Every journalist. Every regulator. Every curious civilian. Excluded not by a lock but by their own incomprehension, which is a considerably more elegant mechanism.
The people who remained — the researchers who know where to bring their work, the government procurement officers who know where to send their encrypted inquiries — needed no price list to remind them of the terms. The decade of conspicuous operation had already done that work. The credential was established. The relationships were in place. The window display had served its purpose and was retired.
Zerodium did not close. A June 2025 report placed ransomware affiliates actively procuring exploits through the broker network Zerodium anchors. The operation continues. It has simply stopped being visible to anyone who was never supposed to be looking in the first place.
Mary Shelley called her novel Frankenstein; or, The Modern Prometheus — the subtitle doing the heavier theological work, naming the precise nature of the transgression. What Zerodium built across a decade of operation is not unlike what Prometheus stole: a capability that belonged, in the minds of those who wielded institutional power, exclusively to the gods. The theft was not the hard part. The hard part was standing in the open afterward, fire in hand, and daring anyone to take it back.
No one did.
The website is a PGP key. The fire is still burning.
The Invoice
The transaction begins, always, with a demonstration.
A researcher — talented, likely operating alone, probably working across a setup that would not look out of place in a graduate student's spare bedroom — has found something. A flaw in the architecture of a widely deployed system. A gap between what the software believes it is doing and what can actually be done to it. In the language of the industry, a zero-day: a vulnerability whose existence is unknown to the people responsible for patching it. The clock on its value starts running the moment it is found, and runs in only one direction.
The researcher contacts Zerodium. What follows is not a negotiation in any conventional sense. Zerodium does not pay for theories. It does not pay for partial chains, for promising leads, for proof-of-concept code that demonstrates a vulnerability exists without demonstrating that it can be weaponised. What Zerodium pays for is a working exploit — functional, reliable, deployable against a real target in a controlled environment. The demonstration happens first. The money follows.
This sequence deserves more attention than it typically receives. At the moment the researcher demonstrates the exploit — at the precise moment the weapon is shown to work — Zerodium has seen it. They have watched it operate. The technical knowledge of how it functions now exists in their hands as well as the researcher's. The wire transfer that follows is real and the contract is enforceable, but the fundamental asymmetry of the transaction has already resolved itself entirely in Zerodium's favour. They hold the weapon before they pay for it. In no conventional arms market does this dynamic hold. It is the kind of arrangement that is only possible when one party's word is backed by sufficient institutional weight that the other party accepts the risk without flinching.
The payment itself arrives by wire transfer. This is worth noting not because it is surprising — it is the obvious mechanism — but because of what it accomplishes culturally. A wire transfer is among the most bureaucratically normal things that can happen between two parties. Invoices are generated. Bank details are exchanged. Compliance boxes are ticked. A researcher who has just handed a sovereign government the ability to silently compromise the devices of anyone it chooses receives, in return, a transaction indistinguishable from a consulting payment. The moral weight of the exchange is laundered not through any deliberate deception but through the mundane procedural language that surrounds it. The paperwork does not lie. It simply declines to characterise.
What the researcher agrees to, beyond accepting payment, is exclusivity. The vulnerability cannot be disclosed to the software vendor who might patch it. It cannot be sold to another buyer. It belongs to Zerodium — and this exclusivity is not a contractual formality. It is the load-bearing pillar of the entire commercial architecture, for a reason that is worth sitting with carefully.
A zero-day is a zero-day precisely because it is unknown. Its value — to a government, to an intelligence agency, to anyone operating in the space where offensive capability determines outcomes — derives entirely from the fact that the target does not know the door is open. The moment a second party deploys the same exploit against a different target, the probability of detection by the vendor doubles. The moment a third party uses it, the weapon has become a liability with a shortening fuse. Distribute a zero-day widely enough and you have not sold a weapon. You have sold a countdown timer.
This logic determines the entire shape of Zerodium's client-side revenue model, and it is worth understanding precisely because it is almost never discussed precisely.
Zerodium's government clients did not, in all likelihood, purchase individual exploits like items from a catalogue. They subscribed — at a publicly stated minimum of half a million dollars annually — to what Zerodium termed its Zero-Day Research Feed. But what the subscription actually purchased requires careful parsing. The most plausible reading of the architecture — and the one that the internal logic of the zero-day market most strongly supports — is that the subscription fee was not the price of access to the weapons themselves. It was the price of admission to the room where the weapons were described.
The subscription client knows what is in inventory. They know what capabilities exist, against which platforms, with what reliability. They know what their adversaries could theoretically acquire. This is itself enormously valuable intelligence — a nation-state that knows a critical iOS zero-click exists in Zerodium's catalogue has learned something significant about the current state of the attack surface, regardless of whether it ever purchases the exploit itself.
The exploit itself — the actual weapon, the deployable capability — is where the second transaction occurs. And here the pricing logic becomes extraordinary, because the nation-state purchasing exclusive access to a zero-day is not only paying for the capability. It is paying for the guarantee that its adversaries cannot have it. Exclusivity, in this context, is not a premium feature. It is the entire point. The NSA does not want the FSB holding the same key. French intelligence does not want German intelligence running the same zero-click against a shared target. The value of denial — the value of knowing that the capability is yours and no one else's — is, for a state-level client, potentially as significant as the value of the capability itself. Zerodium can price accordingly.
The revenue architecture that falls out of this model is, from a purely commercial standpoint, elegant. The subscription base provides guaranteed recurring income regardless of whether any client ever converts a catalogue browse into an exclusive acquisition. The per-exploit exclusivity transactions provide high-margin variable revenue, priced not against the cost of development but against the geopolitical stakes of the specific capability. The inventory risk — the possibility that an exploit is patched by the vendor before it can be sold exclusively — is absorbed by Zerodium, which is why the subscription model matters: it insulates the operation from the degradation of any individual asset. If an iOS zero-click is burned by an accidental vendor discovery before a client pulls the trigger on exclusivity, Zerodium's subscription revenue continues regardless.
The researcher, meanwhile, has signed away any further interest in where the capability goes. The exclusivity agreement formalises an ignorance that was always going to be total — they will not know which government bought the weapon, against which targets it was deployed, or what it found when it got there. The contract makes this official. The ignorance is the product, packaged and sold along with everything else.
Shelley's Victor Frankenstein kept meticulous notebooks. The science was documented. The methodology was recorded. What he did not write down — what the notebooks conspicuously omit — is any serious engagement with the question of what the creature would do once it existed. That was someone else's problem. The work was its own justification.
The invoice had been paid. The creature had its own ideas about where it was going.
What a Modern Day "SPECTRE" Might Look Like
Ian Fleming invented SPECTRE in 1961 as a narrative convenience. The Cold War had produced a spy fiction problem: a villain who was straightforwardly Soviet could not be used in American film markets, and a villain who was straightforwardly American created diplomatic difficulties the Bond producers had no appetite for. The solution was an organisation with no ideology, no national allegiance, and no geopolitical loyalty whatsoever. SPECTRE — the Special Executive for Counter-intelligence, Terrorism, Revenge and Extortion — existed for one purpose only: to identify the gap between what competing powers wanted and what they were positioned to do about it, insert itself into that gap, and charge accordingly.
Fleming understood, perhaps better than he intended to, that this was not a fantasy. It was a structural prediction.
The prediction runs as follows. Nation-states require capabilities they cannot always develop internally, procure openly, or acknowledge publicly. The gap between what a state needs and what it can be seen to be doing is not a failure of the system — it is a feature of it, produced deliberately by the political and legal architecture that governs state behaviour. That gap does not go unfilled. It attracts, with the reliability of a physical law, private actors willing to operate in the space between legality and exposure, between legitimate commerce and criminal enterprise, between the light and whatever lies immediately adjacent to it. Those actors, if they are sophisticated enough, do not need to be controlled by the states they serve. They need only to be useful to them. Usefulness, sustained over time, becomes its own form of protection.
Zerodium was launched in 2015 by Chaouki Bekrar, who had previously run a French company called VUPEN doing essentially identical work at a lower profile. VUPEN's client list, when it became partially visible, included the NSA. This is not inference or allegation — it is documented. The American signals intelligence apparatus was a paying customer of the company whose founder then built Zerodium. The supply chain did not change. The branding did.
From 2015 to late 2024, Zerodium operated with a visibility that was, in the context of the industry it occupied, extraordinary. The price list was public. The acquisition programme was documented. The founder gave interviews. The company had a LinkedIn page and a Delaware incorporation and all the surface features of a legitimate commercial enterprise, which in the strictly legal sense it was. No serious regulatory action was taken against it in any jurisdiction. Not in the United States, where its operations were centred. Not in France, where its founder was based. Not in any of the Five Eyes jurisdictions whose citizens' devices were among the targets of capabilities Zerodium brokered.
The question this raises is not complicated, but it is one that the mainstream coverage of Zerodium consistently declined to press. The Wassenaar Arrangement — the multilateral export control regime that governs dual-use technologies including intrusion software — was amended in 2013 specifically to address this class of tool. The amendment was substantially weakened before implementation following lobbying from precisely the entities whose procurement pipelines depended on the market remaining open. The states with the power to regulate Zerodium out of existence were the states writing Zerodium's subscription checks. The conflict of interest was not incidental. It was the architecture.
This is the point at which the Fleming comparison stops being a literary observation and starts being a structural one. SPECTRE's genius, in the novels, was not its evil. Plenty of fictional organisations are evil. SPECTRE's genius was its indispensability — the way it had arranged itself so that the people most capable of dismantling it had the strongest reasons not to. Blofeld did not need to threaten governments into leaving him alone. He simply needed them to keep needing what he sold. The threat was implicit in the dependency, and the dependency was the product.
Zerodium did not need to threaten anyone either. It needed only to remain the most efficient mechanism available for moving high-grade offensive capability from the researchers who found it to the governments that required it. The NSA, running on government salaries and bureaucratic procurement timelines, could not compete on acquisition speed or price. The criminal underground, lacking institutional banking relationships and the ability to offer eight-figure annual subscription arrangements, could not compete on trust or scale. Zerodium occupied the gap between them with the precision of something that had been designed to fit it — which, structurally, it had.
Whether the design was deliberate in any conspiratorial sense is the wrong question, and it is the question that serious analysis of this space consistently gets distracted by. The right question is simpler: does the observable behaviour of Zerodium differ, in any material respect, from what we would expect to observe if it were a privately incorporated signals intelligence procurement vehicle operating with the tacit sanction of one or more Western intelligence services?
The answer, having surveyed the available evidence, is: almost nothing would look different.
The company was incorporated in Delaware. The founder was French. The predecessor company sold to the NSA. The regulatory frameworks that might have constrained the operation were quietly defanged. The company operated openly for nearly a decade without legal consequence. And then, in January 2025, it replaced its entire public presence with an encryption key — the digital equivalent of a number that rings somewhere you are not supposed to know about, answered by people who already know who you are.
Fleming's SPECTRE kept an octopus as its symbol. The choice was not arbitrary. The octopus has no skeleton. It can pass through any gap large enough to admit any part of it, and the rest follows. It has no fixed form. It is as intelligent as it needs to be and no more visible than it chooses to be. It leaves no trace that cannot be attributed to something else.
The symbol, it turns out, was the most accurate thing about the fiction.
The Client Problem
Chaouki Bekrar has said, in various formulations over the years, that Zerodium sells exclusively to government clients in North America and Europe. This statement has been repeated in press coverage with a frequency that has, through sheer repetition, acquired a patina of verification it does not possess. It is a policy declaration made by the chief executive of a private company whose financial interest is served by the policy sounding responsible. The mechanism by which it might be audited does not exist. The entity to whom Bekrar is accountable for the accuracy of this claim is Bekrar.
This is not, in itself, an accusation of dishonesty. It is an observation about the epistemic structure of the claim. In the absence of a client list, a regulatory filing, an independent audit, or any mandatory disclosure mechanism, "North America and Europe, government clients only" means precisely what any unverifiable assertion means: we are invited to weigh it against whatever else we know about the environment in which it was made.
To understand what the client relationship actually looks like, it helps to understand what the subscription buys — and what it does not. A government agency paying the minimum half-million dollar annual retainer has not purchased a weapon. It has purchased a seat at the table where the weapons are described. The subscription is intelligence about the intelligence: what capabilities exist, against which platforms, at what reliability. A nation-state that knows a critical iOS zero-click is sitting in Zerodium's inventory has learned something operationally significant regardless of whether it ever moves to the second transaction. It knows the door is open. It knows what getting through that door would cost. It can make decisions accordingly.
The second transaction — the exclusive acquisition of a specific capability — is where the real commercial and geopolitical weight of the model becomes visible. And here the logic that governs zero-day value asserts itself with a precision that no amount of policy language can soften. A zero-day distributed to multiple clients ceases, by definition, to be a zero-day. Deploy the same iOS zero-click across three separate government operations against three separate targets and you have tripled the probability of vendor detection, tripled the probability that a compromised device surfaces in a forensic investigation, tripled the probability that the capability is burned — not for one client but for all of them simultaneously. The weapon destroys itself through overuse. The exclusivity is not a commercial premium. It is the technical precondition of the weapon's continued existence as a weapon.
This means that what a nation-state is purchasing when it moves from subscription to exclusive acquisition is not only a capability. It is a denial. The NSA acquiring exclusive access to a given zero-click has simultaneously ensured that the FSB cannot have it. French intelligence locking down a WhatsApp exploit has ensured that German intelligence cannot deploy the same tool against a shared target. The value of that denial — the geopolitical weight of knowing that a specific offensive capability is yours and no one else's, for as long as the vendor remains unaware — is, for a state-level client operating in an environment of active adversarial competition, potentially as significant as the capability itself. Zerodium understands this. The exclusivity pricing reflects it.
What we actually know about the government client base comes primarily not from Zerodium but from the 2015 breach of Hacking Team — a different company, a different founder, a different name, but the same market, the same moral logic, and the same category of assurance about the responsible stewardship of offensive capability. When Hacking Team's internal systems were compromised and their client data exposed, the list that emerged included Sudan, Ethiopia, Bahrain, Azerbaijan, Kazakhstan, and Saudi Arabia. These were not rogue purchases made in violation of company policy. They were clients. The invoices were in the system. The relationships were maintained. The assurances about responsible use had been made and accepted and everyone had moved on.
Hacking Team was not Zerodium. The point is not guilt by association. The point is that the gap between "Western governments only" and "governments" has, in the one case where internal documentation became available, turned out to be wherever the money was. The subscription model, if anything, makes this gap easier to obscure — a government that pays an annual retainer for catalogue access and never converts that access into an exclusive acquisition leaves almost no transactional record that a compliance review could locate. The subscription is the relationship. The relationship is deniable in ways that individual exploit purchases might not be.
There is a further dimension to the client problem that the "Western governments only" framing obscures entirely, and it is the dimension that matters most to the people whose devices are being targeted. Western governments are not a morally homogeneous category. The Five Eyes intelligence alliance conducts mass surveillance programmes whose scope and legal basis remain, decades after the Snowden disclosures, subjects of active litigation in multiple jurisdictions. Law enforcement agencies in Zerodium's declared client pool have used commercial spyware against journalists, lawyers, and political opponents — not in authoritarian states, but in European Union member countries, documented by researchers at Citizen Lab and Amnesty International with a specificity that has survived legal challenge. The question of whether a given Zerodium acquisition ended up on a dissident's phone or a journalist's laptop is not answered by confirming that the purchasing government was headquartered in a democracy. It is answered by knowing what the capability was used for — information that exists nowhere in the public record and is protected, in most relevant jurisdictions, by state secrecy provisions that place it beyond any oversight mechanism that might otherwise apply.
The chain of accountability between the moment of researcher discovery and the moment of operational deployment runs through Zerodium's acquisition process, through the subscription client's catalogue access, through the exclusive acquisition transaction, through the client's internal procurement and targeting authorisation, and finally to the device of whoever is being surveilled. Each link in that chain is opaque. Each transition between links is protected — by contract, by classification, by the structural invisibility that the subscription model specifically produces. This is not a design flaw. It is the design.
In June 2025, a report documented ransomware affiliates — specifically the group tracked as FIN12 — procuring exploits through the broker network that Zerodium anchors. If accurate, this represents a failure of end-user vetting that Bekrar's policy claims cannot accommodate. It also suggests something about the porousness of the boundary between the subscription client pool and the wider exploit market — a porousness that the two-tier model, for all its commercial elegance, does not eliminate. A zero-day that has been exclusively acquired by a government client and then stolen, leaked, or resold downstream is still a zero-day, briefly, until the vendor patches it. The fuse shortens. The damage accumulates. The original transaction is long since complete.
The monster does not stay in the room where it was handed over. It never has.
The Protection Paradox
There is a question that serious coverage of Zerodium has consistently approached and then declined to ask with full precision. It is not a complicated question. It is this: in a world governed by export control regimes, financial crime statutes, arms trafficking legislation, and the full apparatus of national security law that Western states have spent seventy years constructing and refining — how does a private company operate an international market in offensive weapons, openly, for nearly a decade, and remain entirely untouched by any of it?
The available answers sort themselves into three categories. The first is regulatory incompetence — the relevant authorities simply did not understand what Zerodium was doing, or lacked the legal tools to act on that understanding. The second is deliberate tolerance — the relevant authorities understood perfectly well and chose not to act, for reasons that served their interests. The third is something closer to what, in any other context, would be called sponsorship — the relationship between Zerodium and the intelligence apparatus of one or more Western states is not merely one of vendor and client but something with more structure to it, more deliberate architecture, more mutual benefit consciously arranged.
The first answer can be disposed of quickly. The people responsible for export control enforcement in the United States and the European Union are not naive about the exploit market. The NSA's Tailored Access Operations unit, GCHQ's National Cyber Security Centre, and their counterparts across the Five Eyes alliance employ some of the most sophisticated technical analysts in the world. The idea that these institutions failed to understand what Zerodium was selling, to whom, and at what price is not credible. The price list was public. The business model was documented in the open press. Zerodium was not operating in shadow. If anything, its conspicuous visibility was the most striking feature of its existence.
The second answer is more honest and more uncomfortable. The Wassenaar Arrangement's 2013 amendment on intrusion software — the most plausible mechanism through which Zerodium's operations might have been constrained — was weakened significantly before implementation. The lobbying effort that produced this weakening was conducted by, among others, entities whose government clients depended on the exploit pipeline remaining open. The amendment that emerged from this process created obligations narrow enough that Zerodium's model sat comfortably outside them. This was not an accident of drafting. Legislative language of this kind does not become conveniently narrow by coincidence. It becomes conveniently narrow because the people with the strongest interest in its narrowness are also the people with the most direct access to the people doing the drafting.
The NSA's documented history as a paying client of VUPEN — Zerodium's direct predecessor, same founder, same model — is the fact that the second answer rests on most securely. An intelligence agency that has been a paying customer of a vendor does not typically lead the charge to regulate that vendor out of existence. It has a supply chain interest in the vendor's continued operation. It has a relationship interest in not antagonising a source of capability it relies on. It has, in the most basic institutional sense, every reason to ensure that the regulatory environment around that vendor remains permissive, and no compelling reason to do otherwise.
This is not corruption in any simple sense. It does not require backroom arrangements or explicit agreements. It requires only the alignment of institutional interests that is the normal operating condition of the relationship between government procurement and private defence contracting everywhere it exists. The defence contractor stays in business because the government keeps buying. The government keeps buying because the contractor provides something it needs. The regulator, who is often the same institutional entity as the procurer, finds reasons not to disrupt the supply chain. The system is self-reinforcing and requires no conspiracy to sustain itself — only the ordinary operation of incentive structures that everyone involved understands and none of them need to discuss.
The third answer is the one that the available evidence neither confirms nor rules out, and that its unfalsifiability makes simultaneously the most interesting and the most dangerous to assert. It is the answer that asks whether Zerodium's relationship to Western intelligence is not merely one of tolerated vendor but of something with more intentional design — a privatised procurement mechanism, incorporated at arm's length, that allows state actors to acquire offensive capability without the accountability that attaches to direct government development of the same tools. The In-Q-Tel model, which the CIA has used openly since 1999 to invest in private technology companies whose products serve intelligence purposes, demonstrates that this kind of arrangement is not hypothetical. It is standard practice, conducted in the open, in the venture capital market. A covert version of the same logic applied to the exploit acquisition market would be structurally indistinguishable, from the outside, from what Zerodium has always appeared to be.
What makes the third answer difficult to dismiss is precisely what makes it difficult to confirm: the observable evidence is identical under all three hypotheses. A company that is merely tolerated looks the same, from the outside, as a company that is deliberately protected. A company that is deliberately protected looks the same as a company that is, at some level of the beneficial ownership structure, an instrument of the entities protecting it. The layering of Delaware incorporation, European founder, predecessor company relationships, and selective regulatory inaction produces an ambiguity that is, itself, the most useful feature of the arrangement — whatever the arrangement actually is.
In January 2025, when Zerodium replaced its website with a PGP key, the trade press noted the change with mild puzzlement and moved on. What the change actually represented — the retirement of a decade-long credential, the completion of a transition from visible market-maker to invisible infrastructure — was not discussed in those terms, because discussing it in those terms requires sitting with a conclusion that the normal frameworks of technology journalism are not well equipped to accommodate. The conclusion is this: the protection paradox is not a paradox at all. The absence of regulatory action against Zerodium is not a mystery requiring explanation. It is the most legible feature of the entire operation — the thing that, once you have looked at it directly, tells you most precisely what kind of thing you are looking at.
Fleming put it simply, as he usually did when he was being most acute. SPECTRE did not survive because it was powerful enough to defeat the forces arrayed against it. It survived because the forces arrayed against it had decided, each for their own reasons, that survival served them better than defeat. The organisation existed in the space that decision created. It furnished that space tastefully. It charged whatever the market would bear.
The market, it turned out, would bear a great deal.

The Researcher's Bargain
They are not villains. This is the first thing to establish, and the most important, because the alternative framing — the one that casts the vulnerability researcher who sells to Zerodium as a knowing participant in whatever harm eventually flows downstream — is both morally convenient and analytically useless. It is convenient because it locates the ethical failure at the point of individual choice, which is the point furthest from institutional power and therefore the point where accountability is cheapest to assign. It is useless because it explains nothing about why the market exists, who structured it, and who benefits most from the arrangement by which a brilliant person working alone absorbs the moral weight of decisions made by entities with orders of magnitude more power and information than they possess.
The researchers who sell to Zerodium are, by any reasonable assessment, among the most talented technical minds in their field. The capability Zerodium pays two and a half million dollars for is not found by accident. It is produced by sustained, sophisticated, genuinely creative work — the kind of work that requires holding an enormously complex system in mind simultaneously, perceiving the gap between its intended behaviour and its actual behaviour, and then constructing a reliable method of exploiting that gap under real-world conditions. This is hard. The people who can do it reliably are rare. They are also, for the most part, operating in a market whose terms they did not set and whose structure they did not design.
The alternative available to a researcher who has found a critical zero-day in iOS or Android is, in principle, responsible disclosure — contacting Apple or Google directly, reporting the vulnerability through the vendor's bug bounty programme, and accepting whatever the vendor chooses to pay. Apple's maximum bug bounty payout is one million dollars, for a zero-click kernel code execution vulnerability with specific conditions attached. Google's is lower. These are not trivial sums. They are also, compared to Zerodium's acquisition prices, less than half the available market rate for equivalent capability — paid by the entity with the greatest interest in patching the vulnerability, which means the capability is neutralised rather than weaponised, and the researcher receives credit rather than anonymity.
Here the internal logic of the zero-day market delivers its sharpest observation about the researcher's position. The exclusivity the researcher signs away is not merely a contractual formality. It is, as Section II establishes, the technical precondition of the weapon's value. A zero-day that has been disclosed to the vendor has been destroyed as a weapon — patched, neutralised, converted from offensive capability into a CVE number in a security advisory. A zero-day held exclusively by a single government client retains its full value precisely because the vendor remains ignorant. The researcher, by accepting Zerodium's terms, is not merely selling a capability. They are selling the continued ignorance of the people responsible for protecting the billions of users whose devices the capability can compromise. That ignorance is the product. The exclusivity agreement makes its maintenance contractually mandatory. The researcher's own subsequent ignorance — about clients, targets, deployments, consequences — mirrors, at the individual level, the systemic ignorance that their work is specifically purchased to preserve.
The environment in which this choice is made has been deliberately structured by Western governments through selective regulatory inaction and the systematic defanging of legal frameworks that might otherwise have altered the economics of the decision. The researcher making this choice is not operating in a moral vacuum of their own construction. They are operating in a market whose terms were set by the same institutions that are also, simultaneously, the end consumers of the capability they are being asked to sell at a discount. The vendor bug bounty programme exists in a regulatory environment carefully maintained to ensure it never becomes the only available option. The gap between the bug bounty payout and the Zerodium acquisition price is not a market inefficiency. It is a subsidy — paid by researchers — for the maintenance of an offensive capability pipeline that serves state interests while locating moral exposure at the point furthest from state power.
There is also the question of what responsible disclosure actually accomplishes in practice. A vulnerability disclosed to Apple or Google is patched — eventually, through a process that takes weeks or months, during which the vulnerability exists in the wild in the hands of anyone else who has found it independently. The patch is pushed to devices whose owners may or may not install it, on timelines that vary by manufacturer, carrier, and geography, leaving the population of vulnerable devices elevated for months after the official fix is released. The moral satisfaction of responsible disclosure is real. Its practical effect on the security of the devices it is supposed to protect is considerably more complicated than the ethical framing suggests.
None of this is an argument for selling to Zerodium. It is an argument for looking at the full architecture of the situation rather than the narrowest available slice of it. The researcher who accepts two and a half million dollars via wire transfer, signs the exclusivity agreement, and walks away from a conversation they will never be able to have about where the capability goes — that researcher has made a choice with genuine moral content. They have also made a choice within a structure designed, by actors far more powerful than they are, to make that choice as economically rational and as morally invisible as possible. The contract formalises the ignorance. The ignorance is, as it has always been, the product.
What the researcher cannot see — what the structure is specifically designed to prevent them from seeing — is the end of the chain they have just joined. They will not know which government subscribed and then converted that subscription into an exclusive acquisition of their specific capability. They will not know which operation it was deployed in. They will not know whose phone was compromised, whose communications were read, whose location was tracked, whose network was penetrated. They will not know whether the capability was used once and retired or stockpiled and eventually stolen — as NSA tools were stolen, and released into the wild to become the substrate of attacks against hospitals and infrastructure and the ordinary digital lives of people who have no part in any of this and no way of knowing they are downstream of a transaction that happened in a spare bedroom somewhere, between a talented person doing difficult work and a company with a Delaware incorporation and, until recently, a very clean website.
The open book in Von Holst's frontispiece — the one lying face-up in the dirt at Frankenstein's feet, already irrelevant now that the creature breathes — is the researcher's notebook. The methodology is documented. The exploit is proven. The wire transfer is processing.
Whatever happens next is someone else's problem.
The contract says so.
What Fiction Understood First
Ian Fleming did not think of himself as a prophet. He thought of himself as an entertainer — a man who had spent the war years in Naval Intelligence and emerged with a precise understanding of how power actually operated, which he then transmuted into fiction because fiction was the only form in which that understanding could be published without consequences. The Bond novels are not escapism. They are a report, lightly disguised, from someone who had sat in the rooms where the decisions were made and noticed things that the official record was not designed to preserve.
What Fleming noticed, and encoded in the architecture of SPECTRE, was that the most durable form of power is not the kind that announces itself. States announce themselves. Armies have flags. Intelligence agencies have budgets, however classified, that appear somewhere in the apparatus of government accountability. The entity that operates in the gap between these structures — that sells to all of them, answers to none of them, and derives its protection from the very competition it profits from — has a kind of immunity that formal power can never quite purchase. It is immune because it is useful. It persists because its persistence is, for each of the powerful actors who might otherwise dismantle it, preferable to the alternative.
Fleming put an octopus on SPECTRE's banner because the octopus was the right symbol. Not the shark, which is fast and visible and dies when you pull it from the water. Not the spider, which builds a fixed structure and is findable at its centre. The octopus: boneless, formless, capable of passing through any gap that admits any part of it, intelligent enough to solve problems it has never encountered before, invisible when it chooses to be, and possessed of the useful quality that when it is finally seen, it is usually already too late.
The symbol was the most accurate thing about the fiction. The fiction was more accurate than most of the journalism.
Zerodium operated for nearly a decade in conditions that should, by any normal analysis, have attracted the kind of regulatory and legal attention that closes operations down. It did not close down. It published a price list for weapons and ran an international market in offensive capability and incorporated in Delaware and gave interviews and maintained a LinkedIn page and paid researchers via wire transfer and sold subscriptions to government intelligence agencies for half a million dollars a year and experienced, across the entire span of its visible operation, zero serious legal consequences in any jurisdiction on earth. And then, having established itself so thoroughly that it no longer needed a window display, it took the window down and left an encryption key in its place and continued operating in a form that a ransomware affiliate was documented procuring from as recently as last year.
This is not the behaviour of a company that got lucky with regulators. This is not the behaviour of a company that slipped through a gap in the law through inadvertence or good fortune. This is the behaviour of a company that understood, from the moment of its founding, that the gap it occupied was not a regulatory oversight but a deliberate structure — maintained by the entities that needed it maintained, protected by the interests that required its protection, and available to whoever had the institutional credibility to operate within it without threatening the arrangement that made it possible.
Mary Shelley understood the same thing from a different angle. The creature in Frankenstein is not the monster of the film adaptations — lurching, inarticulate, destroyed by its own violence. The creature in the novel is intelligent, articulate, and entirely rational. It does what it does because the structure of its situation makes its behaviour logical. It was called into being by someone who wanted the capability it represented without thinking seriously about the consequences of its existence. It was abandoned when its creator found the reality of what he had made more confronting than the idea of it had been. It survived, and acted, and caused the damage it caused, not because it was evil in any simple sense but because the world it had been introduced into had no framework for dealing with what it was — and the person most responsible for that introduction had structured the situation, whether consciously or not, to ensure that the consequences would fall on everyone except himself.
The invoice had been paid. The notebook was closed. The creator had moved on to other problems.
Bekrar has moved on too. Or moved inward. The website is a PGP key. The price list is gone. The LinkedIn page still exists, because LinkedIn pages are the kind of thing that persists after everything else has been taken down, a digital fossil of a period of conspicuous operation that served its purpose and was retired. What remains is infrastructure — the relationships, the reputation, the decade of established trust with clients who know how to send an encrypted email and researchers who know what the going rate is and do not need a published price list to tell them.
The monster is not in the laboratory anymore. It has not been in the laboratory for a long time. It is out in the world, in forms that are difficult to trace back to their origin, doing things that are difficult to attribute to the transaction that made them possible, causing damage that is real and measurable and almost never connected, in any public accounting, to the spare bedroom and the wire transfer and the exclusivity agreement and the Delaware incorporation and the clean professional website that has since been replaced by thirty lines of cryptographic text and an email address.
What fiction understood first, and what the decade of Zerodium's visible operation has now demonstrated in sufficient empirical detail to constitute something approaching proof, is that the most dangerous markets are not the ones that hide. They are the ones that operate in plain sight, sustained by the tacit consent of the powerful, protected by the very interests they serve, visible to anyone who looks directly at them and structurally invisible to the oversight mechanisms that are supposed to be looking.
The website was zerodium.com. It had clean typography. It had a price list. It had a LinkedIn page.
It was, in any honest accounting, an international arms market — operating openly, for nearly a decade, because the people with the power to close it had decided, each for their own reasons, that it was more useful open.
The window is down now. The fire is still burning.
The creature walks among us still.
Jonathan Brown (A.A.Sc., B.Sc) writes about cybersecurity infrastructure, privacy systems, the politics of AI development and many other topics at bordercybergroup.com and aetheriumarcana.org. Border Cyber Group maintains a cybersecurity resource portal at borderelliptic.com . He works from a custom-built Linux platform (SableLinux™) which is currently under development and fully documented at https://github.com/black-vajra/sablelinux.
If you would like to support our work, providing useful, well researched and detailed evaluations of current cybersecurity topics at no cost, feel free to buy us a coffee! https://bordercybergroup.com/#/portal/support
Member discussion: